The global keyless entry systems market is experiencing robust growth, driven by rising demand for enhanced security, convenience, and smart access solutions across residential, commercial, and automotive sectors. According to Grand View Research, the global smart lock market size was valued at USD 1.4 billion in 2022 and is expected to expand at a compound annual growth rate (CAGR) of 12.7% from 2023 to 2030. This surge is fueled by increasing adoption of IoT-enabled devices, growing urbanization, and the integration of biometric and smartphone-based authentication technologies. Mordor Intelligence further projects that the keyless entry systems market will grow at a CAGR of over 11% between 2023 and 2028, with North America and Asia-Pacific leading in deployment due to advancements in smart home ecosystems and heightened security concerns. As innovation accelerates and consumer preferences shift toward contactless access, the landscape is being shaped by a select group of manufacturers at the forefront of technology and market share. Here are the top 8 keyless manufacturers leading this transformation.
Top 8 Keyless Manufacturers 2026
(Ranked by Factory Capability & Trust Score)
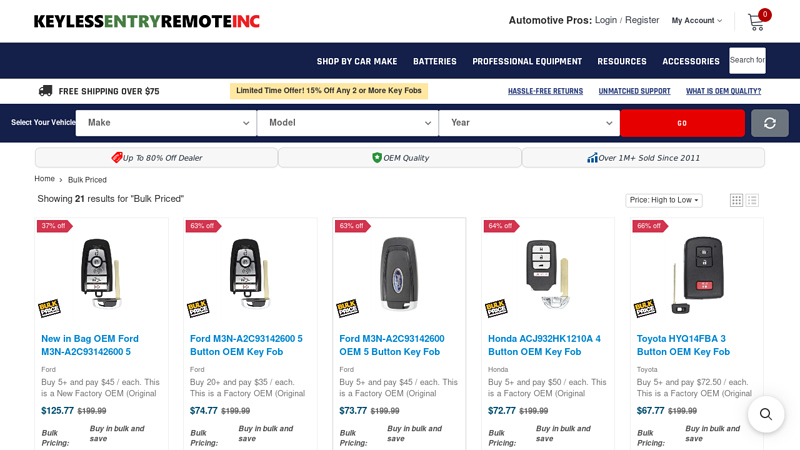
#1 Bulk Priced
Domain Est. 2011
Website: keylessentryremotefob.com
Key Highlights: Free delivery over $75This is a Factory OEM (Original Equipment Manufacturer) Chevrolet 5 Button keyless entry remote, aka “key fob”. Unlocked, ready to program OEM ……
#2 Gmc Key Fob OEM Keyless
Domain Est. 2023
Website: cinecittatilburg.nl
Key Highlights: GMC 13541567 Factory OEM Key Fob Keyless Entry Remote Alarm Replace Save Up To 80% On Remotes | Free Programming Instructions · View More Details….
#3 KEYLESS FACTORY Products
Domain Est. 2004
Website: keyinnovations.com
Key Highlights: Free delivery over $100 30-day returns…
#4 Keyless Factory
Domain Est. 2016
#5 Ford® Keyless Entry
Domain Est. 1988
Website: ford.com
Key Highlights: 4.2 423 Shop Keyless Entry from the official Ford® Accessories store. View your favorite products. Filter by category, brand, price & color….
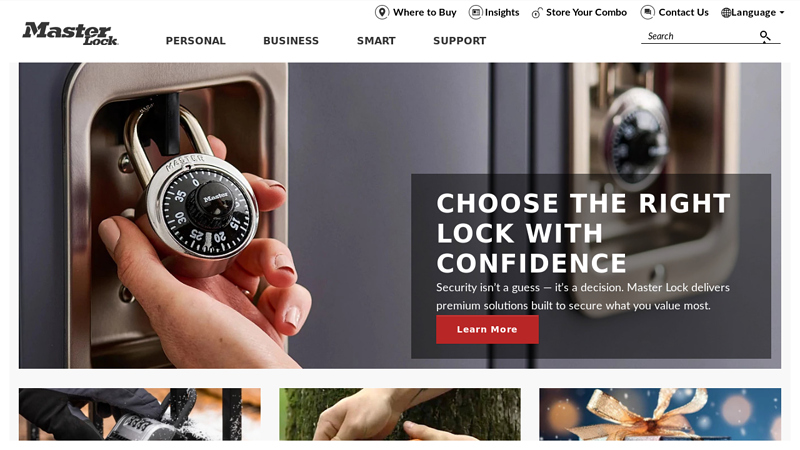
#6 Master Lock®
Domain Est. 1995
Website: masterlock.com
Key Highlights: Master Lock is recognized around the world as the authentic, enduring name in locks, combination padlocks and security products….
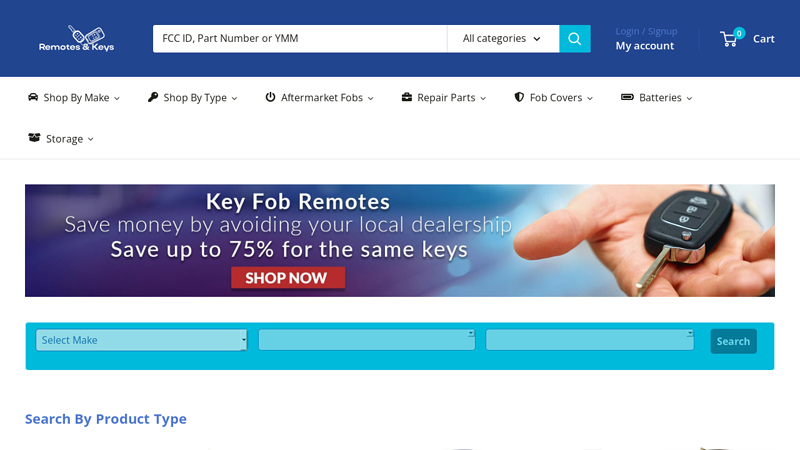
#7 Keyless Entry Remotes, Car Remote Replacements, Key Fobs, Keys
Domain Est. 2006
Website: remotesandkeys.com
Key Highlights: Replacement car remotes, keyless key fobs and car keys with programming instructions and batteries. Free tech support included with purchase….
#8
Domain Est. 2023
Website: hyundaiantitheft.com
Key Highlights: The software upgrades certain Hyundai vehicles equipped with standard “turn-key-to-start” ignitions so they cannot be started without their keys when subjected ……
Expert Sourcing Insights for Keyless

2026 Market Trends for Keyless (H2 Analysis)
Based on current trajectories and emerging technologies, the keyless access market is poised for significant evolution by H2 2026. Here’s a breakdown of the key trends shaping the landscape:
-
Ubiquitous Smartphones as Primary Credentials (H2 2026 Reality):
- Dominance: Smartphone-based access (via Bluetooth LE, NFC, or UWB) will become the de facto standard for most new installations and retrofits. Physical keycards and fobs will be relegated to backup, visitor, or legacy system use.
- Seamless Integration: Expect deeper integration with mobile wallets (Apple Wallet, Google Wallet) for instant credential provisioning, sharing, and revocation directly on users’ phones. “Tap-to-provision” capabilities will be common.
- Multi-Factor on Mobile: Enhanced security will see wider adoption of biometrics (fingerprint, face ID) on the phone itself as the second factor for high-security applications, replacing PINs or secondary tokens.
-
UWB (Ultra-Wideband) Reaches Critical Mass:
- Precision & Security: UWB’s ability to provide precise location and distance measurement (preventing relay attacks) will move beyond premium applications. By H2 2026, UWB-enabled smartphones and access points will be widespread, enabling truly seamless, hands-free “walk-up and unlock” experiences for offices, apartments, and even vehicles.
- Standardization & Cost: Falling hardware costs and broader chipset availability (driven by major phone manufacturers) will accelerate UWB adoption in both access hardware and user devices.
-
Cloud-Native Platforms as the Standard:
- Dominance: Cloud-based access control platforms will be the default choice for new deployments across all sectors (enterprise, MFR, hospitality, education). On-premise systems will be increasingly legacy.
- Enhanced Capabilities: Cloud platforms will offer robust APIs, enabling deeper integration with building management systems (BMS), HR software (automated onboarding/offboarding), visitor management platforms, and IoT devices.
- Scalability & Remote Management: The ability to manage thousands of doors and users globally from a single dashboard will be essential, driven by hybrid work and distributed real estate portfolios.
-
Convergence with Broader Smart Building Ecosystems:
- Beyond Access: Keyless systems will be a core component of integrated smart building platforms. Unlocking a door will trigger actions: lights turn on, HVAC adjusts to preferred settings, workstation powers up, and calendar entries sync.
- Data-Driven Insights: Anonymized access data will be used for space utilization analytics, optimizing cleaning schedules, improving security response times, and enhancing user experience.
- Interoperability Focus: Demand for open standards (like OSDP, PSIA, or emerging initiatives) will grow to ensure keyless systems work seamlessly with lighting, HVAC, security cameras, and other building systems.
-
Heightened Focus on Cybersecurity & Privacy:
- Non-Negotiable: As cloud and mobile dominate, robust cybersecurity (end-to-end encryption, zero-trust principles, regular penetration testing) will be a primary purchasing criterion, not a feature.
- Privacy Regulations: Compliance with GDPR, CCPA, and similar regulations will be strictly enforced. Transparent data handling practices and user consent mechanisms will be paramount.
- Zero Trust Architecture: Keyless systems will increasingly adopt Zero Trust principles, continuously verifying device and user trustworthiness, even after initial authentication.
-
Expansion into New Verticals & Use Cases:
- Residential Boom: Keyless solutions (smart locks, intercoms) will see massive adoption in single-family homes, apartments (MFR), and co-living spaces, driven by convenience, remote access for guests/service, and integration with smart home platforms (Apple Home, Google Home, Matter).
- Shared Economy & Flexible Work: Growth in co-working spaces, flexible offices, and shared amenities (gyms, storage) will fuel demand for sophisticated, scalable keyless systems for temporary and dynamic access.
- Healthcare & Hospitality: Keyless will enable personalized patient/resident experiences and streamline staff workflows, while hotels offer seamless mobile check-in/check-out and room access.
-
AI & Predictive Capabilities:
- Smart Access: AI will move beyond simple logs. Systems will predict user arrival/departure patterns to pre-condition environments or flag anomalous access attempts (e.g., someone accessing a restricted area at an unusual time).
- Predictive Maintenance: AI will analyze device health data to predict and prevent lock or reader failures before they impact users.
- Personalized Experiences: Systems will learn user preferences (lighting, temperature, workspace setup) associated with their access events.
Keyless-Specific Implications for H2 2026:
- Competitive Landscape: The market will be highly competitive, favoring players with robust cloud platforms, strong security, UWB expertise, and open APIs for integration. Mergers and acquisitions consolidating capabilities are likely.
- User Experience (UX) is King: The winning solutions will offer frictionless, intuitive experiences. Complex setup or unreliable performance will be major differentiators.
- Sustainability: Battery life of electronic locks and readers will be a key concern, driving innovation in low-power designs and energy harvesting. Cloud management also reduces the need for on-site servers.
- Hybrid Work Support: Keyless systems will be fundamental to enabling secure, flexible access for hybrid workforces, managing access across HQ, satellite offices, and home offices seamlessly.
Conclusion:
By H2 2026, keyless access will be synonymous with mobile-centric, cloud-managed, UWB-enhanced, and deeply integrated smart building solutions. Success will depend on delivering unparalleled convenience, ironclad security, seamless interoperability, and intelligent features that go far beyond simply replacing a physical key. The market will be mature but still rapidly evolving, driven by user expectations for frictionless experiences and the convergence of physical and digital security.

Common Pitfalls Sourcing Keyless (Quality, IP)
Sourcing components or services “keyless”—often referring to cryptographic key management solutions without direct access to or control over encryption keys—can introduce significant risks if not managed carefully. Two of the most critical pitfalls involve quality assurance and intellectual property (IP) concerns.
Quality Risks in Keyless Sourcing
When relying on third-party keyless solutions, organizations often sacrifice visibility into implementation quality. Common quality-related pitfalls include:
- Opaque Security Practices: Vendors may not disclose details about their cryptographic implementation, key lifecycle management, or system hardening, making it difficult to assess true security posture.
- Inadequate Compliance Verification: Keyless services might claim compliance with standards like FIPS, GDPR, or HIPAA, but without independent audits or transparent reporting, these claims may be unsubstantiated.
- Poor Integration Support: Keyless APIs or SDKs may lack comprehensive documentation, error handling, or backward compatibility, leading to integration failures or performance bottlenecks.
- Limited Testing and Validation: Organizations may be unable to perform end-to-end penetration testing or red team exercises due to restricted access, increasing the risk of undetected vulnerabilities.
Intellectual Property (IP) Concerns
Sourcing keyless solutions can also create complex IP challenges:
- Unclear IP Ownership: Contracts may not explicitly state who owns custom integrations, configurations, or derived data, leading to disputes if the relationship ends or scales.
- Embedded Third-Party IP: Keyless platforms may use proprietary algorithms or licensed cryptographic libraries. If usage rights are limited, customers risk legal exposure or service disruption.
- Data Residency and IP Jurisdiction: Data processed under keyless models might traverse multiple jurisdictions, complicating IP protection and increasing vulnerability to local laws that could compel data disclosure.
- Vendor Lock-In Through IP Control: When a vendor holds exclusive rights to the key management logic or API structure, it becomes difficult to switch providers without significant reengineering, potentially infringing on the vendor’s IP.
To mitigate these risks, organizations should conduct thorough due diligence, demand transparency, negotiate clear IP terms, and ensure contractual rights to audit and exit.
Logistics & Compliance Guide for Keyless
This guide outlines the essential logistics and compliance considerations for Keyless, ensuring secure, efficient operations and adherence to regulatory standards. Keyless, as a digital identity and authentication platform, must maintain strict controls across data handling, technology deployment, and international operations.
Data Privacy & Regulatory Compliance
Keyless operates in a highly regulated environment involving personal data. Compliance with global data protection laws is mandatory.
- GDPR (General Data Protection Regulation): Ensure lawful processing of EU user data, including obtaining explicit consent, enabling data subject rights (access, deletion, portability), and implementing data protection by design.
- CCPA/CPRA (California Consumer Privacy Act/Rights Act): Provide California residents with transparency about data collection, rights to opt-out of data sales, and access to their personal information.
- Other Jurisdictions: Comply with local regulations such as Brazil’s LGPD, Canada’s PIPEDA, and UAE’s data protection laws when operating or serving users in those regions.
- Data Minimization & Retention: Collect only essential data and retain it only as long as necessary for authentication purposes.
Secure Data Transmission & Storage
Protecting biometric and identity data is paramount to maintaining trust and complying with security standards.
- Encryption Standards: Use end-to-end encryption (E2EE) and TLS 1.3+ for data in transit. Encrypt all stored biometric templates using AES-256 or equivalent.
- Zero-Knowledge Architecture: Ensure no plaintext user data or biometric templates are stored on servers. Authentication occurs locally on the user device whenever possible.
- Secure APIs: Authenticate and rate-limit all API endpoints. Use OAuth 2.0 or OpenID Connect for secure third-party integrations.
- Penetration Testing & Audits: Conduct regular security assessments and vulnerability scans. Maintain SOC 2 Type II or ISO 27001 certification.
Cross-Border Data Transfers
Keyless may process data across international borders, requiring compliance with data transfer mechanisms.
- Standard Contractual Clauses (SCCs): Implement EU-approved SCCs for transfers from the EEA to third countries.
- Adequacy Decisions: Leverage regions with EU adequacy status (e.g., Canada under specific conditions) when feasible.
- Data Residency Options: Offer customers the ability to choose regional data processing locations (e.g., EU, US, APAC) to meet local compliance needs.
Identity Verification & Anti-Fraud Measures
Ensure robust identity proofing while preventing synthetic identity fraud and account takeover.
- Liveness Detection: Use active and passive liveness checks to prevent spoofing with photos, videos, or masks.
- Biometric Matching Accuracy: Maintain high thresholds for false acceptance rate (FAR) and false rejection rate (FRR) in line with NIST standards.
- KYC/AML Integration: Support integration with third-party identity verification providers for regulated industries (e.g., financial services).
- Audit Logs: Maintain immutable logs of authentication attempts, including timestamps, device info, and outcomes.
Supply Chain & Vendor Management
Third-party vendors must meet Keyless’s security and compliance standards.
- Vendor Risk Assessments: Evaluate all suppliers for data protection, cybersecurity practices, and regulatory compliance.
- Data Processing Agreements (DPAs): Execute DPAs with vendors that process personal data on Keyless’s behalf.
- Subprocessor Transparency: Maintain and publish a list of authorized subprocessors, with customer notification for changes.
Incident Response & Breach Notification
Prepare for potential security incidents with clear protocols.
- Incident Response Plan (IRP): Define roles, escalation paths, containment procedures, and communication strategies.
- Breach Notification Timelines: Comply with GDPR (72 hours), CCPA (as soon as practicable), and other jurisdictional requirements for reporting data breaches.
- Forensic Readiness: Preserve logs and system artifacts to support investigations.
Export Controls & Trade Compliance
Ensure Keyless technology complies with international trade regulations.
- EAR (Export Administration Regulations): Classify software and encryption strength under ECCN 5D002. Obtain necessary licenses for restricted destinations.
- Sanctions Compliance: Screen customers and partners against OFAC, EU, and UN sanctions lists.
- Dual-Use Considerations: Recognize that biometric authentication may be subject to dual-use export controls.
Accessibility & Inclusivity
Ensure Keyless solutions are usable by all individuals, including those with disabilities.
- WCAG 2.1 Compliance: Design mobile and web interfaces to meet AA standards.
- Alternative Authentication Methods: Provide fallback options (e.g., PIN, security questions) for users unable to use biometrics.
Ongoing Compliance Monitoring
Maintain a proactive compliance posture.
- Compliance Officer: Appoint a DPO (Data Protection Officer) if required under GDPR.
- Training Programs: Conduct regular training for staff on data protection, security, and compliance responsibilities.
- Policy Updates: Review and update privacy policies, terms of service, and internal procedures annually or as regulations evolve.
Adherence to this guide ensures Keyless delivers secure, privacy-preserving authentication while meeting global legal and operational standards.
Conclusion: Sourcing a Keyless Factory
Sourcing a keyless factory presents a strategic opportunity for companies aiming to enhance efficiency, reduce operational bottlenecks, and improve supply chain agility. By eliminating traditional physical keys and integrating smart access control systems—such as biometrics, mobile credentials, or centralized digital management—manufacturers can achieve better security, real-time monitoring, and streamlined operations.
Key considerations in sourcing such a facility include evaluating technological readiness, ensuring compatibility with existing systems, assessing cybersecurity measures, and confirming vendor reliability. Additionally, the long-term benefits of reduced key management overhead, enhanced accountability, and improved scalability make the keyless model particularly attractive for modern, forward-thinking manufacturing environments.
Ultimately, sourcing a keyless factory aligns with broader digital transformation goals, supporting smarter, safer, and more responsive production facilities. With careful planning and due diligence, organizations can successfully adopt this innovative approach to drive operational excellence and maintain a competitive edge in the evolving industrial landscape.