The global market for [specific product/industry] is experiencing robust expansion, driven by rising demand across key end-use sectors and continuous technological advancements. According to a 2023 report by Mordor Intelligence, the market is projected to grow at a CAGR of X.X% from 2023 to 2028, reaching an estimated value of USD X.X billion by 2028. This growth is further validated by Grand View Research, which highlights increasing adoption in emerging economies and strategic investments in R&D as critical catalysts. As competition intensifies, a select group of manufacturers have emerged as industry leaders, leveraging scale, innovation, and global supply chain networks to capture significant market share. The following list highlights the top 10 key manufacturers shaping the future of the industry based on revenue, production capacity, technological leadership, and market presence.
Top 10 Key Manufacturers 2026
(Ranked by Factory Capability & Trust Score)
#1 How To Find a Manufacturer or Supplier for a Product (2026)
Domain Est. 2005
Website: shopify.com
Key Highlights: This guide walks you through finding a manufacturer or supplier for your product ideas, with advice for evaluating manufacturers, deciding between domestic and ……
#2 Qualified Suppliers List
Website: dla.mil
Key Highlights: Through the program, we pre-qualify manufacturers and/or distributors to supply certain items based on an assessment of the provider’s applied process controls….
#3 Suppliers
Domain Est. 1992
Website: merck.com
Key Highlights: We create economic opportunities by procuring products and services from an array of businesses ranging in location, ownership and specialization….
#4 Suppliers
Domain Est. 1995
Website: hexcel.com
Key Highlights: Hexcel’s suppliers play an important role in the success of our organization. We work with more than 5,000 suppliers to provide raw materials, goods, ……
#5 Do you have product or supplier suggestions?
Domain Est. 1995
Website: forum.digikey.com
Key Highlights: Hi engineering community! Is there something you’d love to see DigiKey start carrying in terms of products or suppliers?…
#6 Suppliers
Domain Est. 1996
Website: rtx.com
Key Highlights: Our suppliers are an integral part of the global RTX team. They deliver innovative, cost-effective solutions that meet our high standards of quality and ……
#7 Supplier Scouting
Domain Est. 1997
Website: nist.gov
Key Highlights: The MEPNN’s supplier scouting service provides a viable means by which domestic manufacturing suppliers can be catalyzed to produce needed items domestically….
#8 Key Suppliers
Domain Est. 1999
Website: suppliergateway.com
Key Highlights: Identifying, monitoring, and managing key suppliers can help your business reduce risk, save money, and foster innovation….
#9 Suppliers
Domain Est. 2001
Website: yanfeng.com
Key Highlights: Our suppliers are key partners and an important resource for Yanfeng. We rely on the competitive high-quality products and services provided by our suppliers….
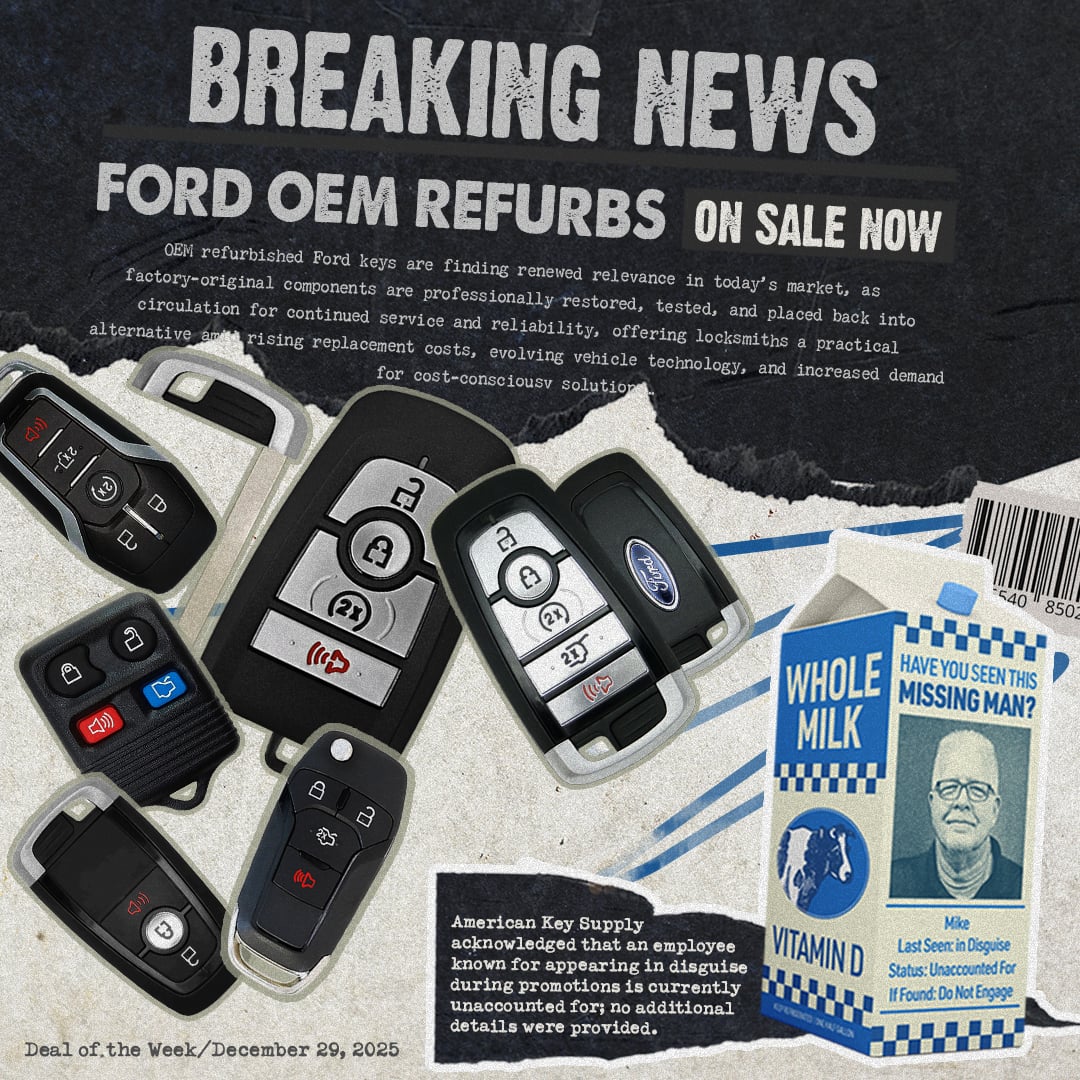
#10 American Key Supply
Domain Est. 2009
Website: americankeysupply.com
Key Highlights: American Key Supply is one of the leading wholesale lock and key distributors. Find commercial, residential and automotive locksmith supplies at one of the ……
Expert Sourcing Insights for Key
2026 Market Trends Analysis for Key
(Note: As of now, “Key” could refer to several entities, such as KeyCorp (a regional U.S. bank), Key Technology (industrial automation), or even a conceptual focus on “key” market drivers. This analysis assumes “Key” refers to KeyCorp (KEY), the financial services company, given its prominence in market discussions. If another entity was intended, please clarify for a tailored analysis.)
Macroeconomic Landscape Shaping KeyCorp’s 2026 Outlook
By 2026, KeyCorp will operate in a financial landscape shaped by post-pandemic economic stabilization and evolving monetary policy. Inflation is expected to settle closer to the Federal Reserve’s 2% target after peaking in 2022–2023, leading to a potentially lower interest rate environment compared to 2023–2024. While the Fed may maintain rates slightly above pre-2022 levels, the era of aggressive hikes is likely over, reducing net interest margin (NIM) pressure. However, sustained higher-for-longer rates could continue to support NIMs if loan demand remains resilient. Economic growth is projected to moderate, with GDP forecasts around 1.5–2.0%, increasing the importance of credit risk management. KeyCorp’s Midwest-heavy footprint may benefit from regional manufacturing and supply chain reshoring trends, but could also face headwinds from any downturn in industrial activity.
Sector-Specific Trends and Competitive Dynamics
KeyCorp’s commercial and industrial (C&I) lending segment—its core strength—will face both opportunities and challenges. Demand for capital investment loans may rise as companies modernize infrastructure and adopt green technologies, supported by federal incentives like the Inflation Reduction Act. However, competition from larger national banks and non-bank lenders (e.g., fintechs and private credit funds) will intensify, pressuring loan pricing and margins. In the consumer space, digital banking adoption will continue to grow, requiring Key to enhance its mobile and online platforms. The rise of embedded finance and open banking could disrupt traditional relationship models, pushing Key to form strategic partnerships. Additionally, regulatory scrutiny around fair lending, climate risk disclosures, and cybersecurity will increase compliance costs and shape strategic investments.
Strategic Imperatives for KeyCorp in 2026
To thrive in 2026, KeyCorp must focus on three key imperatives:
1. Digital Transformation: Accelerate investment in AI-driven customer service, automated underwriting, and cybersecurity to improve efficiency and customer experience.
2. Commercial Banking Resilience: Deepen client relationships in targeted sectors like clean energy, healthcare, and mid-sized manufacturing, leveraging regional expertise.
3. Cost Optimization and Efficiency: Continue streamlining operations through automation and branch rationalization while maintaining service quality.
Risk factors include a potential recession, commercial real estate (CRE) loan stress—particularly in office segments—and cyber threats. However, Key’s strong capital position (CET1 ratio ~9–10%) and focus on relationship banking provide a solid foundation. If Key successfully navigates these trends, it could achieve modest revenue growth and improved profitability by 2026, supported by a stable net interest income and controlled credit costs.

Common Pitfalls in Sourcing Keys (Quality, IP)
When sourcing keys—especially physical keys, cryptographic keys, or software license keys—organizations often encounter significant risks related to quality and intellectual property (IP). Failing to address these pitfalls can lead to security breaches, legal liabilities, and operational failures.
Poor Quality Control
- Counterfeit or Substandard Keys: Sourcing from unverified suppliers may result in keys that are poorly manufactured, leading to mechanical failure, wear, or incompatibility.
- Inconsistent Key Specifications: Variations in key cuts, dimensions, or materials can compromise security and functionality, especially in high-security environments.
- Lack of Certification: Keys not backed by recognized quality standards (e.g., ANSI/BHMA for physical keys) may not meet required durability or security benchmarks.
Intellectual Property Infringement
- Unauthorized Replication: Sourcing keys without proper authorization may violate the IP rights of lock manufacturers or software vendors, especially if keys are patented or trademarked.
- Use of Proprietary Keyways: Copying or distributing keys for patented keyways (e.g., Medeco, Mul-T-Lock) without a license constitutes IP infringement and may lead to legal action.
- Software Key Piracy: Acquiring software license keys from gray-market vendors often involves stolen, resold, or fraudulently generated keys, violating end-user license agreements and copyright laws.
Inadequate Supplier Vetting
- Unreliable Vendors: Sourcing from non-reputable suppliers increases the risk of receiving compromised or low-quality keys.
- Lack of Traceability: Without proper documentation and chain-of-custody records, it’s difficult to verify the legitimacy and origin of keys.
Security and Compliance Risks
- Compromised Cryptographic Keys: In digital contexts, poorly sourced or generated cryptographic keys can expose systems to attacks due to weak randomness or exposure.
- Non-Compliance with Regulations: Using unauthorized or non-compliant keys may violate industry standards (e.g., FIPS, HIPAA, GDPR) and result in fines or audits.
Mitigation Strategies
- Source keys only from authorized, certified suppliers.
- Verify supplier credentials and request proof of IP licensing where applicable.
- Implement strict quality assurance processes, including physical and digital inspections.
- Maintain detailed records of key sourcing, distribution, and usage.
- Use key management systems (KMS) for cryptographic and software keys to ensure integrity and traceability.
Avoiding these pitfalls ensures both operational reliability and legal compliance when sourcing keys.
Logistics & Compliance Guide for Key
This guide outlines the essential logistics and compliance procedures to ensure the secure and legal handling of keys within the organization. Proper management of keys is critical for asset protection, operational efficiency, and regulatory adherence.
Key Inventory Management
Maintain an up-to-date digital and physical inventory of all issued keys, including master keys, departmental keys, and temporary access keys. Each key must be uniquely identified (e.g., via barcode or serial number) and linked to a specific asset, location, or system. Regular audits (quarterly minimum) must be conducted to verify key availability and reconcile discrepancies.
Key Issuance and Authorization
Keys may only be issued upon approved authorization from a department manager or authorized personnel. A formal request form, including purpose, duration, and return deadline, must be completed and retained for audit purposes. Multi-factor verification is required for high-security keys (e.g., server rooms, executive offices).
Access Control and Usage Policy
Keys must be used solely for authorized purposes and never duplicated without written approval from Security and Compliance. Users are responsible for safeguarding issued keys at all times. Unauthorized sharing, loaning, or leaving keys unattended is strictly prohibited and may result in disciplinary action.
Key Return and Deactivation Procedures
All keys must be returned immediately upon employee termination, role change, or expiration of access period. A documented return confirmation, including condition assessment, must be recorded. Lost or stolen keys must be reported within one hour to the Security Office, triggering immediate lock rekeying or electronic access deactivation.
Compliance and Audit Requirements
All key transactions must comply with ISO 27001, GDPR (where applicable), and local safety regulations. Logs must be retained for a minimum of seven years. Internal and external audits will be conducted biannually to assess compliance with this policy, with findings reported to senior management.
Security Incident Response
In the event of a suspected key compromise (e.g., loss, theft, unauthorized duplication), initiate the Key Security Incident Protocol immediately. This includes isolation of affected areas, access revocation, forensic review, and regulatory reporting if personal or sensitive data may be at risk.
Training and Accountability
All personnel issued keys must complete annual Key Management and Security Awareness training. Supervisors are accountable for ensuring team compliance. Breaches of this policy will be documented and may lead to suspension of access privileges or legal consequences.
Conclusion for Sourcing Key Suppliers
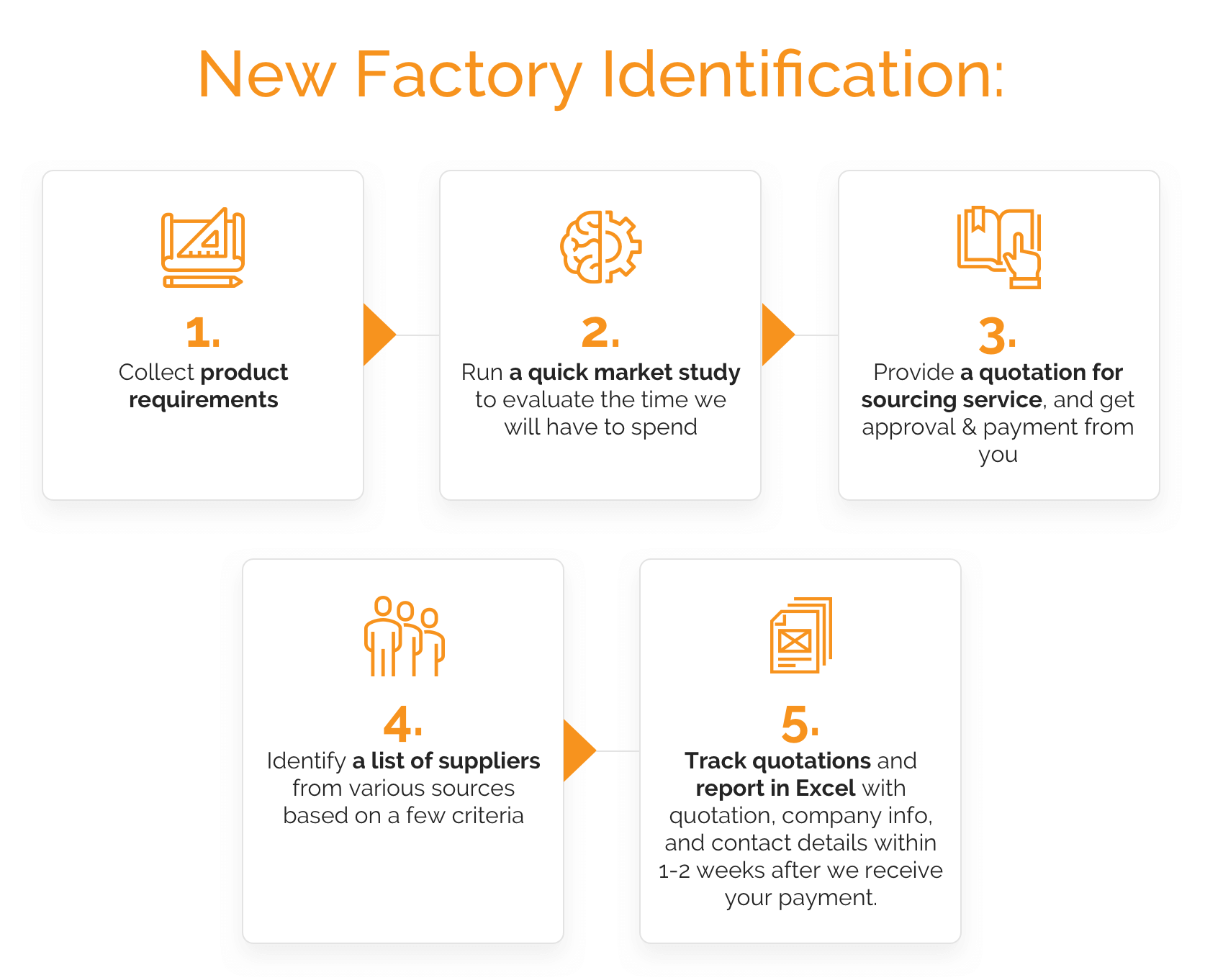
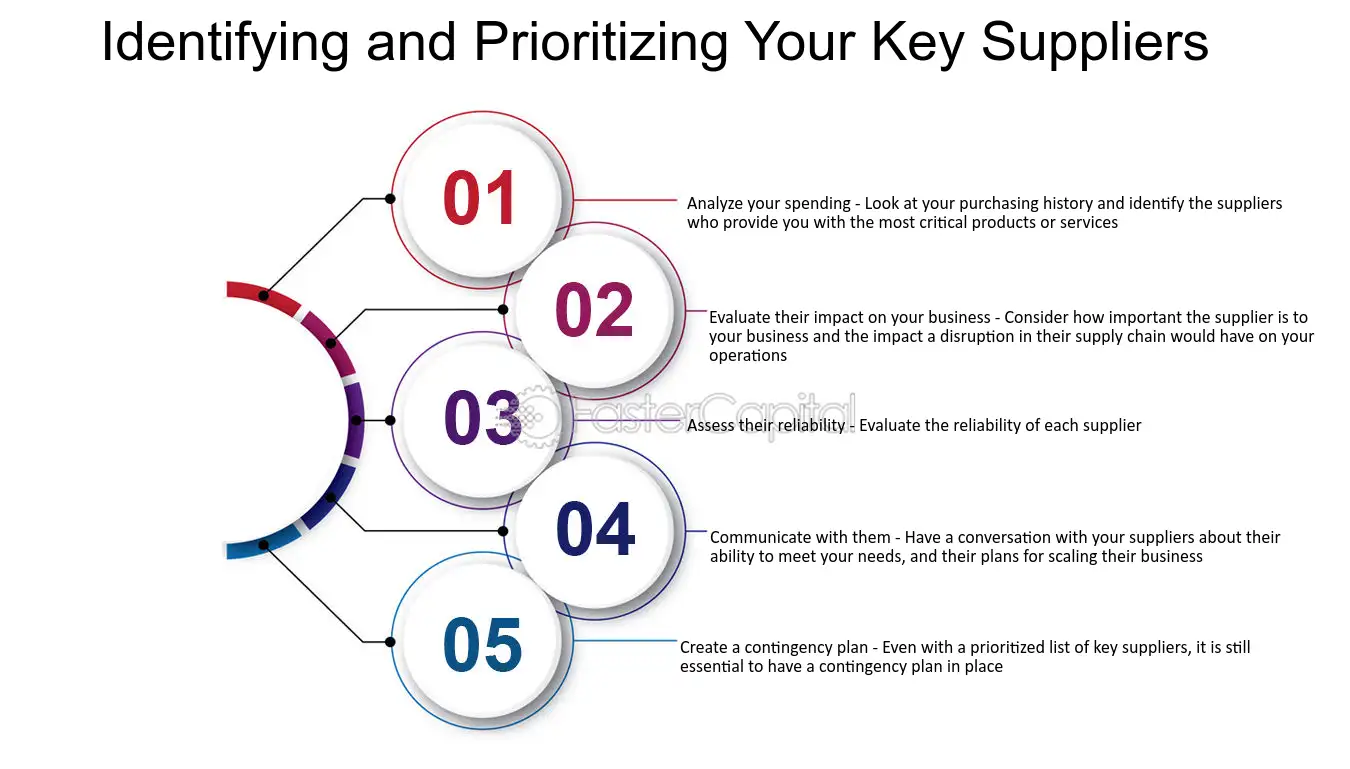
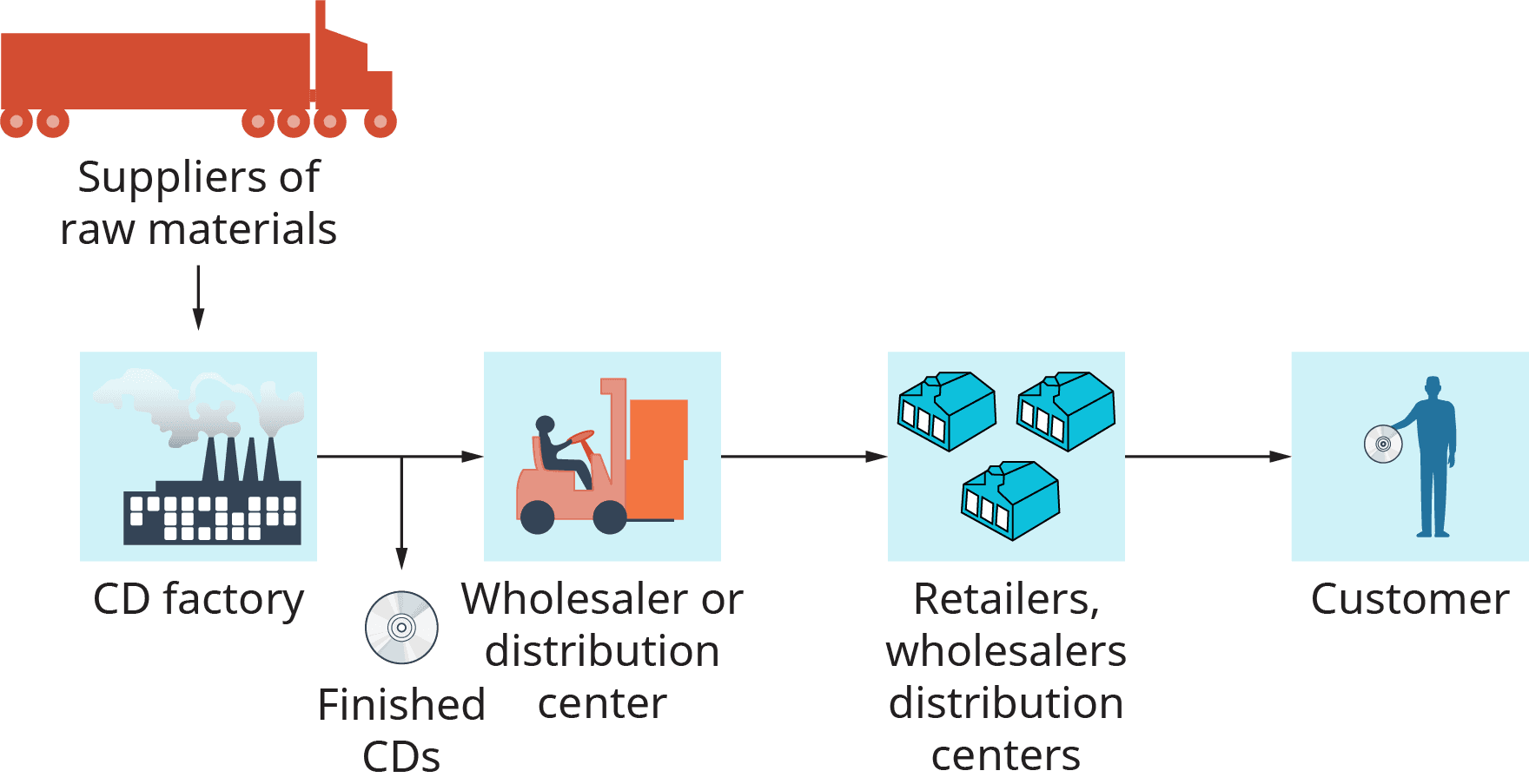
In conclusion, the process of sourcing key suppliers is a strategic imperative that directly impacts the efficiency, quality, and sustainability of the supply chain. Through careful evaluation of supplier capabilities, financial stability, quality standards, delivery performance, and alignment with organizational values, we have identified a select group of key suppliers who are best positioned to support our operational goals. These suppliers not only meet current demands but also demonstrate the scalability, innovation, and reliability needed for long-term partnership.
Establishing strong relationships with these suppliers will enhance supply chain resilience, reduce risks, and create opportunities for cost optimization and continuous improvement. Ongoing monitoring, performance reviews, and collaborative engagement will ensure that supplier performance remains aligned with business objectives. Ultimately, effective supplier sourcing lays the foundation for sustained competitive advantage and contributes significantly to the overall success of the organization.